Security
Enterprise-grade security.
Built from the ground up.
Adapt is a U.S.-based company that adheres to industry best practices, appropriate protections, and smart guardrails to keep your data secure. SOC2 compliant.
Get started freeDesigned to keep your data safe. At every step.
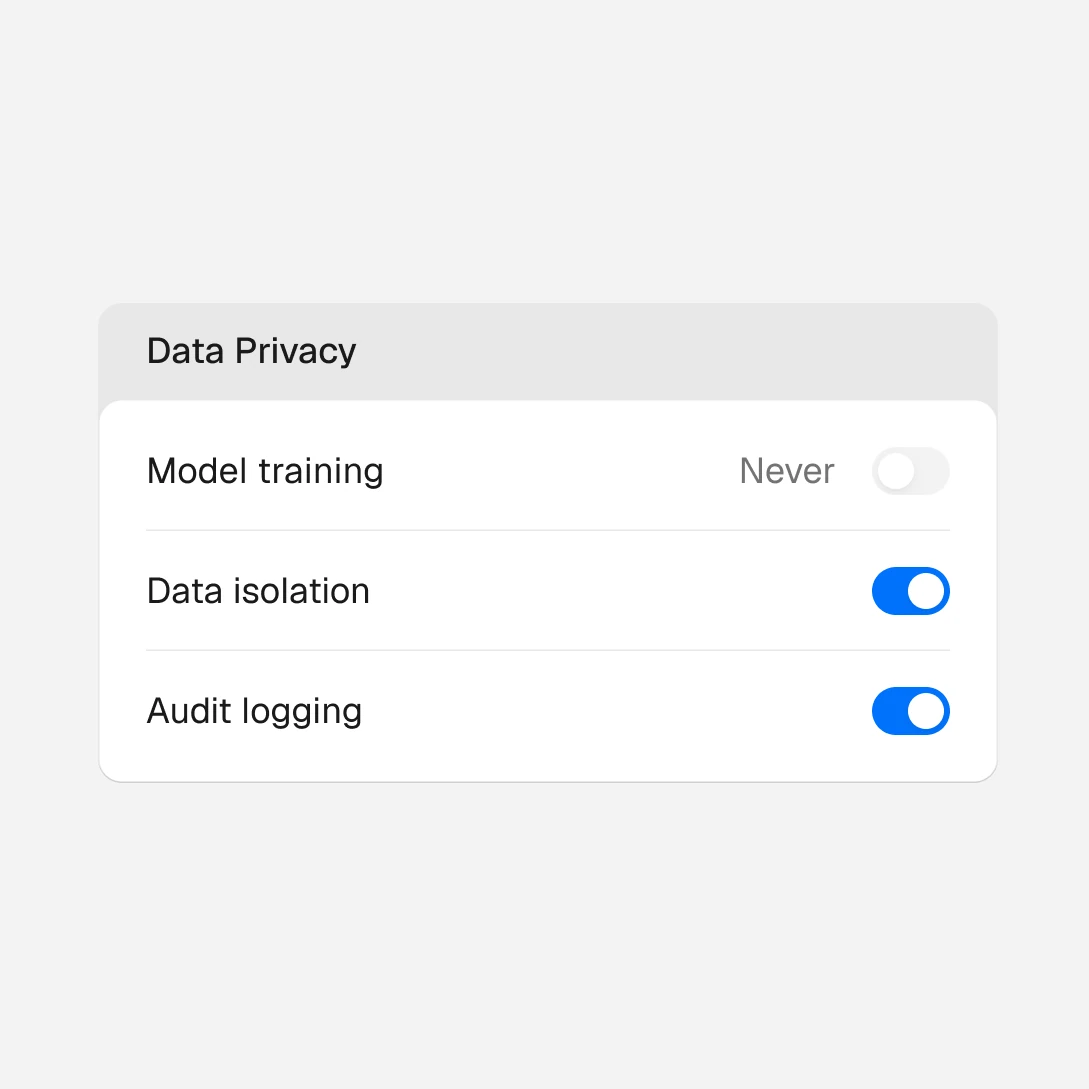
Your data never trains AI models
Your conversations and business data stay in your workspace and are never used for model training.
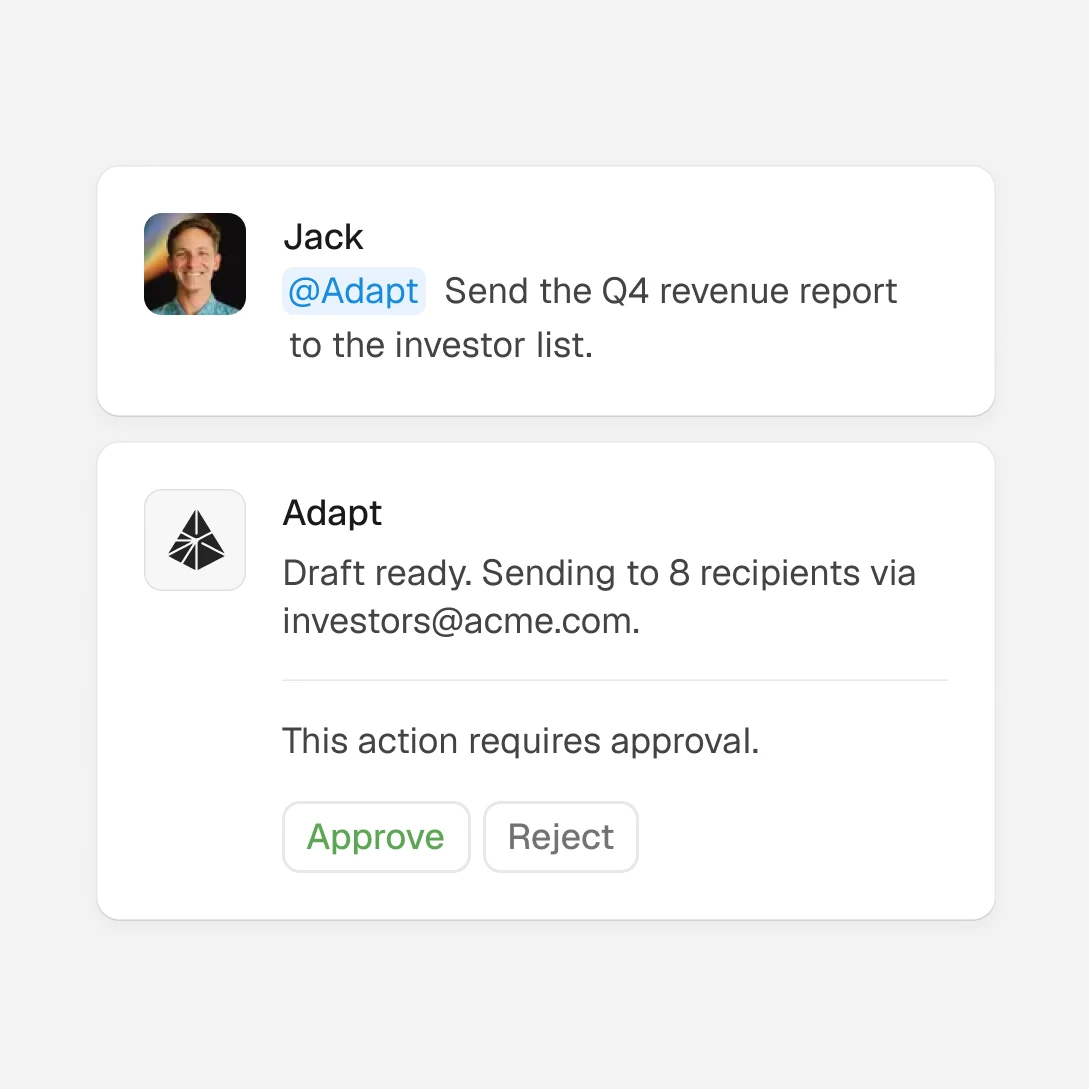
Set policies and permissions
Set company-wide policies to require approval before execution or keep data sources read-only. You stay in control.
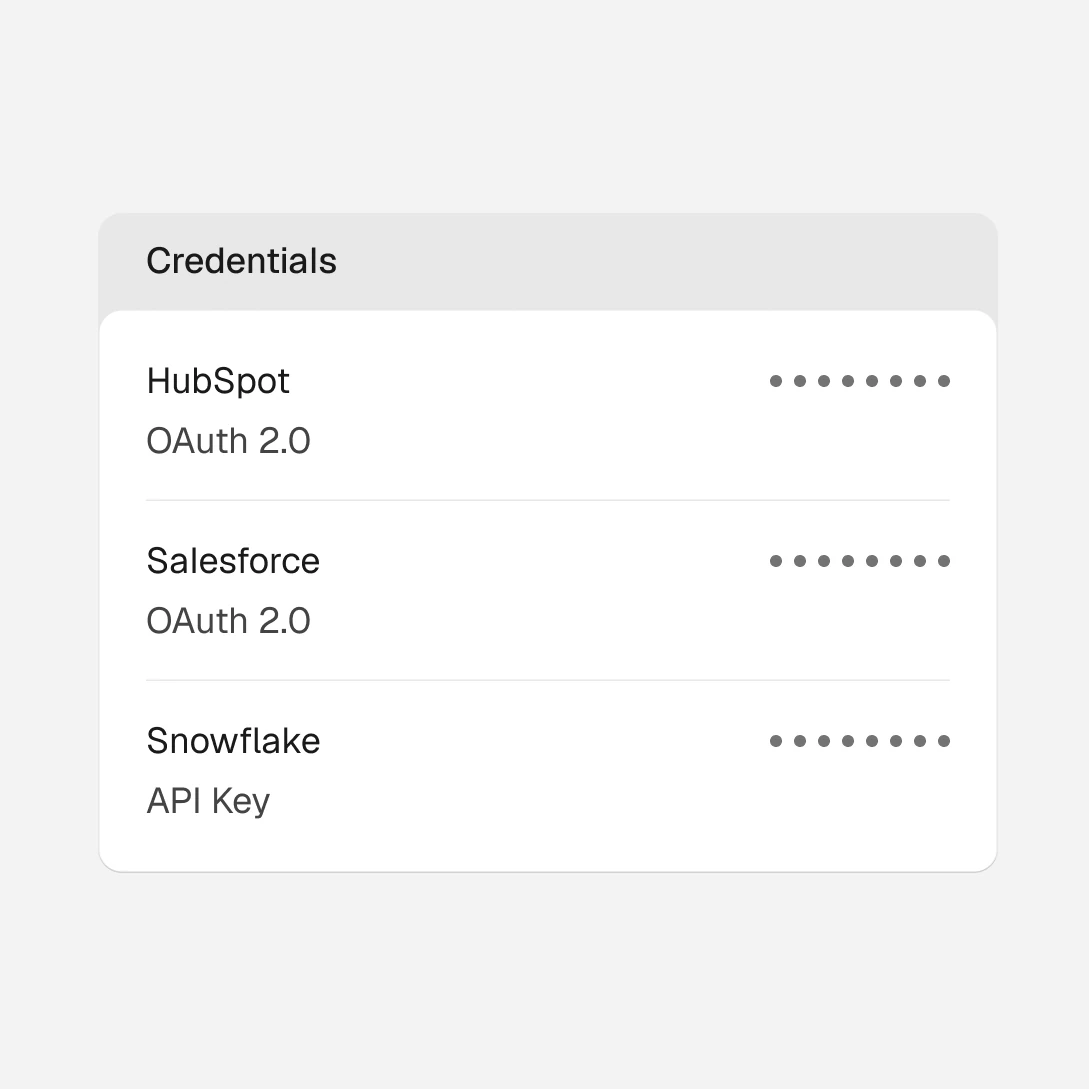
Credentials are encrypted at rest
OAuth tokens and API keys are stored in enterprise-grade infrastructure.
Trust & Compliance
Certified and audited.
Not just promised.
We pursue and maintain the highest standards for trust and compliance so you can deploy Adapt with confidence.
SOC 2
SOC 2 Type I certified. SOC 2 Type II certification currently in progress.
GDPR Aligned
We follow GDPR requirements for data protection, giving you control over your personal data and how it is processed.
CCPA
We adhere to CCPA standards, ensuring California residents have transparency and control over their personal information.
Security Practices
Defense in depth.
At every layer.
Encryption everywhere
All data is encrypted in transit and at rest. Your data is never exposed or accessible to unauthorized parties.
Access controls
Role-based access controls and granular permissions (coming soon) ensure only the right people have access to the right data. Platform access is logged and auditable.
Vulnerability management
Continuous vulnerability scanning and regular penetration testing help ensure our systems stay secure against emerging threats.
Data Handling
Your data.
Your control.
Data isolation
Customer data is logically isolated. Each organization's data is kept separate and is never shared across accounts or used to train models.
Data retention
Data can be deleted on request at any time.
Infrastructure
Hosted on SOC 2 certified infrastructure in the United States. All systems are monitored 24/7.
Vendor management
We maintain a rigorous vendor assessment process. All third-party services are evaluated for security practices and compliance before integration.

Work faster, together.
Across your entire stack.
Get started with up to $300 in credits for you and your team.